DATA SECURITY SOLUTIONS
DATA ENCRYPTION
Over the last decade there has been a big shift in how people tend to work and how they access corporate data and resources. Sensitive corporate and customer data is moving outside the relative safety of the traditional corporate security perimeter – computers on site and within the corporate firewall. Users today want to access information in an increasing number of ways: on personal computers at home, on their own tablets and mobiles, or sharing data through public cloud storage providers. Basically, sensitive data can be found everywhere today.
By the research done by Ponemon Institute (back in 2008!), over 8,000 laptops are being left behind in US airports every week. A large majority of all companies (86%) has had a laptop lost or stolen at some point. The cost of the hardware when losing a laptop is of course not particularly significant – it is the data it contains that holds the real value.
Having data move to so many places and devices outside the direct control of organization creates many different challenges:
• It's becoming increasingly hard and time-consuming to maintain adequate and solid corporate security policies.
• It’s difficult to make sure that all Intellectual Property (IP) stays safe; IP is many times the key asset of a company and usually it’s critical that it is 100% protected.
• If a laptop, smart phone or USB hard disk is lost or stolen it’s very difficult to limit, or even assess, damages. Same thing with decommissioning or when an employee leaves the company. Controlling that she/he can no longer access any corporate data is not easy.
• The challenge of staying compliant. Compliance means to follow the legal obligations and government directives that specify how certain data should be protected. This is becoming proportionally harder the more places users take the sensitive or confidential data.
All of these things must be addressed in one way or another while at the same time ensuring that users remain productive and can continue to work the way they want.
Encryption is widely regarded as one of the most effective ways to protect information from attackers. Security companies have developed tools that make it easy to encrypt data, with streamlined mechanisms that make it virtually transparent to the end user. It is now possible to effortlessly protect corporate information wherever it goes, whether on Windows or Macs, laptops, files uploaded to the cloud, network shares, USB sticks, etc.
Sophos SafeGuard Enterprise
Sophos SafeGuard Enterprise is the complete encryption and data protection solution for companies. It ensures productivity by securing sensitive data wherever it is stored: laptops, USB devices, network shares or even in the cloud, with minimal impact on performance. It manages all devices in the organization from one place and makes regulatory compliance easier with policy enforcement and reporting.
Sophos SafeGuard Enterprise features:
• Centralized key and policy management. Managing encryption keys and policies centrally for all devices and platforms.
• Role-based administration. Administrator roles provide only the privileges they need for their areas of responsibility.
• Auditable management functions. All activities performed in the management recorded for future audit.
• Global client/server communication. Clients are able to communicate with the encryption solution wherever they are in the world.
• Reporting. Provide a mechanism to see the encryption status of the organization from a single console, regardless of operating system.
• Proof of Compliance. Includes mechanism to provide a proof of compliance report in the event of lost.
Sophos SafeGuard Enterprise modules:
• Management Center. Implements and enforces a common, organization-wide security policy framework, providing with a central point of management control in mixed IT environments. Single console to manage full disk encryption, removable media encryption, file share encryption and cloud storage encryption.
• Device Encryption. Transparently encrypts data on laptops, desktops and external media, protecting users against unauthorized access, loss or theft of data. Allows multiple users to share encrypted computers without sharing their passwords. Stops unauthorized users from reading lost or stolen media.
• Data Exchange. Ensures the secure exchange of data on removable media with business partners and customers, even if they don’t have a SafeGuard application installed.
• Encryption for Cloud Storage. Encrypts files uploaded to cloud storage services from managed computers (Dropbox, Google Drive, One Drive, One Drive for Business, Sky Drive, Mediacenter, Egnyte). It also includes readers for opening these files on iOS and Android devices.
• Native Device Encryption. Manages third-party security applications such as Windows BitLocker and Mac FileVault 2 drive encryption.
• Encryption for File Shares. Encrypts user data across workgroups. Protects data on local drives and network servers, at both the file and directory levels.
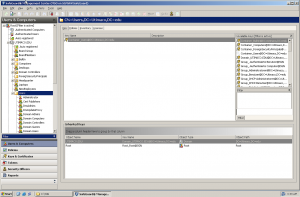
Sophos Safe Guard administrative console
Sophos SafeGuard Enterprise is classified as a leader in Gartner’s Magic Quadrant for the Mobile Data Protection solutions for the year of 2015:
Gartner Magic Quadrant for Mobile Data Protection Solutions