SERVER SECURITY SOLUTIONS
Server Protection
Sophos Server Protection
Sophos Server Protection effectively protects Windows, Linux and UNIX server systems from malicious attacks while keeping servers running at peak performance. Designed to secure mission critical servers, Sophos Server Protection integrates server application whitelisting with advanced anti-malware and HIPS. Sophos Server Protection’s server-based policies provide out-of-the-box protection, giving granular controls for both performance and protection.
• High security, low impact. Innovative features like pre-execution emulation for identifying suspicious behavioral patterns, and in-engine caching, preventing needless rescanning of files between updates. Frequent, lightweight definition updates keeps protection current without causing network congestion. Live Protection looks-up for unknown and suspicious files in real time, keeping servers secure, even between updates.
• Zero-day protection. Sophos Server Protection is the only solution offering cloud-managed server protection integrated with advanced anti-malware, HIPS, and server application whitelisting/lockdown. Servers and data are effectively protected from zero-day attacks.
• One-click Lockdown. Sophos Server Protection is the only solution that achieves lockdown with a single click, securing servers in a safe state. Sophos automatically scans the system, establishes an inventory and whitelists applications. It then locks the connections between applications and associated files, such as dll, data files and scripts. During the lockdown process, Sophos automatically creates trusted change rules to ensure only trusted sources or processes can update the whitelisted applications.
• Prevent in-memory attacks. Other whitelisting applications require extensive manual creation of rules to secure scripts and other system files. Sophos automatically establishes trusted relationships between applications and associated system files, such as scripts, data and DLL files. This process protects the integrity of the applications and prevents malicious in-memory attacks.
• Integrated anti-malware, HIPS and whitelisting. Sophos Server Protection integrates application whitelisting with anti-malware and HIPS, giving the highest level of security. Once the server is locked down, anti-malware and HIPS work to prevent content-based threats (such as an infected PDF or word document) that could otherwise exploit vulnerabilities within whitelisted applications.
Historically, some of the most prolific virus families (e.g., Netsky or SoBig) distributed themselves as file attachments in email. These families relied on users double-clicking an attachment, which would run the malicious code, infect their machine and send itself to more email addresses from that computer.
Nowadays, hackers have changed their focus and mainly use the web for malware distribution. They still use email messages, but mostly as a way of distributing links to malicious sites, not for carrying malicious file attachments. However, even today some malware families use email distribution to run malicious code on user machines.
Companies should use strong anti-spam technology in conjunction with current endpoint security software and updated system operating software.
Sophos Secure Email Gateway
Sophos secure email gateway is an all-in-one solution for email encryption, DLP, anti-spam and threat protection. It provides advanced protection from today’s sophisticated spear phishing attacks and gives you full control over data leaving organization via email.
Sophos Secure Email Gateway Hardware Appliance Device
Sophos Secure Email Gateway features:
• Advanced threat protection. Sophos Time-of-Click protection blocks malicious email URLs, protecting users from stealthy, delayed, spear phishing attacks. Every URL, in every email, is secured. Every time an email link is clicked, on any device, its reputation is checked against cloud-hosted Sophos SXL database. No client software is required, speeding implementation and reducing user disruption. Sophos Sandstorm enhances targeted attack protection, visibility, and analysis. Sandstorm complements advanced antivirus scanning engine to quickly and accurately detect, block, and respond to evasive threats using powerful cloud based, next-generation sandbox technology.
• Quick and easy data protection compliance. Wizard based DLP rules and policy based encryption makes email data protection simple, preventing costly data-loss incidents. Using Sophos built-in lexicon of hundreds of sensitive data types, you can quickly and easily build DLP policies for users or groups. Protect your information by blocking messages containing sensitive data or by encrypting them before they leave the network gateway.
• SPX Encryption. Sophos patent pending simple SPX Encryption is transparent, simple and requires no changes to user workflow. It doesn’t require clumsy and expensive key management or additional software. SPX Encryption simply encapsulates the email content and attachments into a secure encrypted PDF that can’t be hacked or cracked. It allows users to view their encrypted email anywhere: in their preferred email client, in their webmail or on their mobile device.
• Stamp out snowshoe spam and suspicious email content. Sophos sophisticated email filtering protects users from the latest snowshoe spam, identity theft, password scams and more by looking for suspicious content, attachments or URLs. Support for Sender Policy Framework (SPF) and DomainKeys Identified Mail (DKIM) ensures spam and phishing attacks attempting to spoof legitimate sender domains are blocked. You can also block unwanted content and be sure Sophos proven antivirus scanning is catching the latest threats.
• Simplify mail management. Reduce workload with streamlined management console and managed appliances that offer the best of an on-premise appliance with a managed service. Client gets automated updates and Sophos monitors customer appliances remotely to ensure everything’s running as it should.
• Flexible deployment options. Choose from a variety of hardware appliance options or “VMware Ready” virtual appliance. Simple integration with Microsoft Active Directory and eDirectory will have solution up and running with just a few clicks.
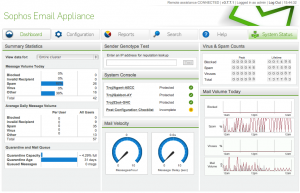
Sophos Email Appliance Administrative Console
Sophos Pure Message for Microsoft Exchange
Sophos PureMessage for Microsoft Exchange guards against e-mail threats such as spam, phishing, viruses and spyware. It controls information sent and received both internally and externally and protects a company against the loss of confidential information or inappropriate use of the email system.
It provides the following features:
• Prevent viruses – Genotype virus detection technology proactively blocks families of viruses even before specific virus signatures are available.
• Code scanning – A range of technologies, including Dynamic Code Analysis, pattern matching emulation and heuristics, automatically check for malicious code.
• Detect and quarantine – Proactively block families of spam campaigns. Sophos genotype spam detection technology detects up to 98% of spam. The intuitive end-user interface and spam digests allows administrator to review quarantine contents.
• Spam blocking – The comprehensive multilanguage spam engine is constantly updated with new spam rules by SophosLabs.
• Centralized management – PureMessage provides an intuitive management console. Manage single or multiple Exchange server deployments from one location.
• Activity monitoring – Administrator can quickly view the status of servers, email throughput and quarantine areas, via the email security dashboard and activity monitor.
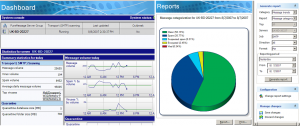
Sophos PureMessage Dashboard and Reports
Corporate policy enforcement features:
• Customizable policies – Sophos policy engine allows you to set email policies to be configured for a specific email direction - inbound, outbound and internal.
• Configurable user rules – Integration with Microsoft Active Directory allows administrator to setup email policy rules for specific users and groups.
• Available policies – Ready-to-use policies can block all file types known to carry potential threats or monitor emails containing offensive language.
• Keyword search – Define policies to search for phrases or regular expressions within emails and attachments, including all common office file formats.
• Secured information – Take advantage of consistent email policy enforcement. Prevent confidential or sensitive information from being accidentally or maliciously emailed outside or within your organization.
In recent years, backing up virtual servers has been another source of headaches for backup administrators. When server virtualization first gained mainstream acceptance, the backup process had a lot of catching up to do. Most backup applications were not virtualization aware, and backup administrators were only beginning to understand the ways in which virtual environments differed from physical server backups.
Initially, most backup administrators chose to back up virtual machines by deploying backup agents to each individual virtual machine. Ultimately, however, this approach proved to be inefficient at best. As virtual machines proliferated, managing large numbers of backup agents became challenging. Never mind the fact that, at the time, many backup products were licensed on a per-agent basis. Resource contention also became a huge issue since running multiple, parallel virtual machine backups can exert a significant load on a host server and the underlying storage.
For that reason, virtual server backups can experience severe bottlenecks when using traditional backup methods that copy data from each virtual machine (VM) as if it were a physical server.
The answer here is to avoid backing up data from the guest VM and instead to deploy backup applications that can copy directly from the host using backup-specific application programming interfaces (APIs). One benefit of running host-based backups is that traditional backup agents can be eliminated, removing a whole set of maintenance and management tasks needed to keep the agents up to date.
Veeam Backup & Replication
Veeam Backup & Replication is an availability, data protection and disaster recovery solution for VMware vSphere and Microsoft Hyper-V virtual environments of any size and complexity.
To provide the most comprehensive protection of your virtual infrastructure, Veeam Backup & Replication complements image-based backup with image-based replication. You can backup any VM, VM container or VM disk, as well as replicate VMs onsite for high availability (HA) or offsite for disaster recovery (DR), across local area and wide area networks.
By leveraging the latest technological advancements of the virtualization technology, Veeam Backup & Replication delivers unprecedented replication speed. It provides near-continuous data protection (or near-CDP) at a fraction of the cost of traditional CDP systems. You can capture changes and update VM images as often as every few minutes as the replication job can be set to run continuously.
Veeam Backup & Replication offers vPower – Veeam’s technology that allows you to:
• Instant VM Recovery. Immediately recover a failed VM, thus reducing downtime of production VMs to the minimum. Instead of making users wait while you provision storage, extract the backup and copy it to production, restart a VM directly from the backup. With Instant VM Recovery, you can recover a failed VM in as little as 2 minutes.
• SureBackup. Verify recoverability of every backup by starting and testing VMs directly from VM backups in an isolated environment.
• Restore guest OS files. Recover a file from any guest OS and file system directly from an image-level backup—without booting the VM, and from virtualized applications with Veeam Explorers for Microsoft Active Directory, Microsoft Exchange, Microsoft SharePoint and Microsoft SQL.
• U-AIR® (Universal Application-Item Recovery). Recover individual objects from ANY virtualized application without agents, additional backups or software tools.
• On-Demand Sandbox. Run VMs from a backup in an isolated Virtual Lab for testing or troubleshooting.
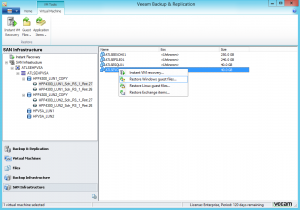
Veeam Backup & Replication Administrative Console