CLOUD SERVICES
CLOUD BACKUP & DISASTER RECOVERY
The purpose of backup is to create a minimum one copy of all data so that a particular file or application may be restored after data is lost, corrupted, deleted or a disaster strikes. Organizing storage space and managing the backup process can be a complicated undertaking. A data repository model may be used to provide structure to the storage. Nowadays, there are many different types of data storage devices that are useful for making backups.
Before data are sent to storage locations, you should consider the following:
• What data (files and folders) to backup.
• What compression method to use.
• How often to run backup.
• What kind of media on which to store the backup.
• Where to store the backup data.
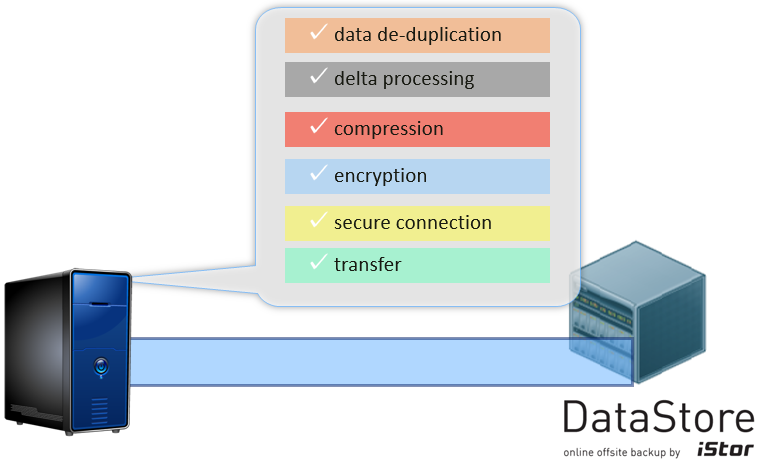
Many different techniques have been developed to optimize the backup procedure. These include optimizations for dealing with open files and live data sources as well as compression, encryption, and de-duplication, among others.
In order to ensure company good name, integrity and longevity, data must be stored in multiple locations; this is no longer only “nice to have”, it is a necessity.
Nowadays reasons for data loss are numerous: fire, flood, earthquake, theft, fraud, destruction, human error, hardware failure, software failure, viruses… More than 35% of all attacks are inside jobs, perpetrated by trusted employees with high security clearance. Backing up to physical media such as external drives, USB, DVD, CD, etc. violate compliance regulations and pose serious security risks as they can easily be lost or stolen. Regardless of how good your hardware and software are and how well you maintain your system, you cannot guarantee that your data will be safe if it’s stored in only one location. As we say in the industry, if it doesn't exist in at least three locations —one of them offsite —it doesn't exist!
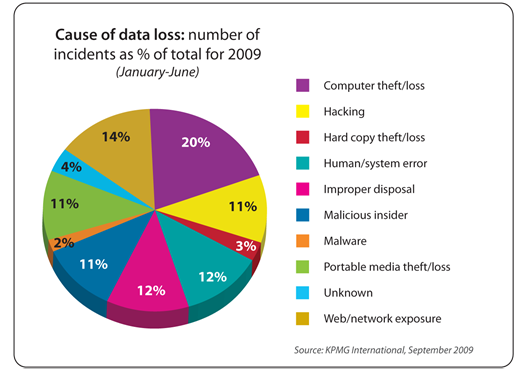
Causes of Data Loss
DataStore Encrypted Cloud Backup
Datastore Cloud backup advantages:
• Capacity based licensing - you can backup unlimited number of servers, workstations and notebooks.
• Low TCO, no capital investment.
• No hardware or software to buy and manage.
• No hardware maintenance cost.
• No software upgrade & maintenance cost.
• No media cost.
How it works:
Datastore Cloud Backup Process
Datastore Disaster Recovery
Disaster recovery consists of the policies and procedures that describe how to recover or continue the technology infrastructure critical to an organization after a disaster. This cryptographic method protects sensitive data by encoding and transforming information into unreadable cipher text. Encoded data may only be decrypted or made readable with a key. Symmetric-key and asymmetric-key are the two primary types of encryption.
Encryption is a type of security that converts data, programs, images, or other information into unreadable cipher. This is done by using a collection of complex algorithms to the original content meant for encryption. Encryption is essential for ensured and trusted delivery of sensitive information.
Symmetric forms of encryption systems make use of a single password to serve as both decryptor and encryptor. Symmetric-key encryption uses two secret, often identical keys or codes for computers involved in message transmission. Each secret key's data packet is self-encrypted. Symmetric types use algorithms that are very safe. One of such type was adopted by the US Government as Advanced Encryption Standard (AES) to store classified information. The Advanced Encryption Standard (AES) is considered more reliable because it uses a 128-bit, a 192-bit or a 256-bit key.
Asymmetric-key encryption, also known as public-key encryption, uses two keys, referred to as a key pair. One is a public key, and the other one is a private key. The public key can be freely shared among various users as it is only meant for encryption. The private key is not shared, and is used to decrypt anything that was encrypted by the public key.
Disaster Recovery as a Service (DRaaS) is a cloud computing and backup service model that uses cloud resources to protect applications and data from disruption caused by disaster. It gives an organization a total system backup that allows for business continuity in the event of system failure. DRaaS is often offered in conjunction with a disaster recovery plan (DRP) or business continuity plan (BCP).
DRaaS enables the full replication and backup of all cloud data and applications while serving as a secondary infrastructure. It actually becomes the new environment and allows an organization and users to continue with daily business processes while the primary system undergoes repair. DRaaS allows these applications to run on virtual machines (VM) at any time, even without a real disaster.
DRaaS advantages are as follows:
• Multisite - resources are replicated to many different sites to ensure continuous backup in the event that one or more sites is unavailable.
• Granular or comprehensive – Depending on customer requirements, if not all data requires backup, an organization can reduce costs with flexibility protection.
• Rapid and Immediate Recovery – with a DRaaS solution in place, if a disaster strikes, you will be able to restore normal operations within minutes.
• Flexibility – various DRaaS services offer clients more options in how to handle different business systems. Any enterprise using DRaaS solutions can select from a variety of recovery scopes, depending on the type of the disaster. These can include server failure, human-caused disasters, loss of power or building access, data hampering, and much more.
• No offsite transportation and storage cost.
• Fast restore for minimal impact on your business.
• You only pay for the storage you use (compressed & deduplicated).
• Supported Applications & Systems.
• Central administration.
Sophos Email
Sophos Email is a cloud email gateway engineered to keep businesses safe from all email threats. It stops spam, phishing, malware and data loss and keeps people productive. It is highly scalable solution with no limitations on user numbers, with datacenters in Frankfurt, Dublin and USA.
Getting started is easy, deployment requires a simple MX record change to route email through Sophos Central. It works with any local email server, and you can simply bring in users and their mailboxes with Active Directory synchronization.
Sophos Email features:
• Instant proven protection. Sophos Email works right out of the box with default settings, giving instant protection for your mailboxes by intercepting all email containing suspicious content, attachments or URLs. Sophos Email uses the latest anti-malware and phishing-detection technology that constantly updates to detect the latest threats. You get phishing and impostor email detection with support for SPF anti-spoofing.
• Simply secure Microsoft Exchange, Office 365, and Google Apps. Shifting email to the cloud doesn’t mean reducing your security. Securing email server or service with Sophos Email ensures trusted email security powered by the SophosLabs global network.
• Goodbye to spam and unwanted mail. Sophos reputation filtering blocks over 99% of spam at the gateway, and anti-spam engine catches the rest, including the latest phishing attacks. Sophos Email filters incoming email by using a variety of advanced detection methods, across many languages.
• Ensure email is always on. When your email server experiences an outage or there’s a disruption to a cloud-based service, Sophos Email automatically queues all incoming mail until the server comes back online. When the service comes back online, all queued mail is delivered, safe and sound. You get automatic alerts, spooling to ensure no mail is ever lost, and an emergency inbox to keep your people productive.
• Empower end users with the self-service portal. Sophos self-service user portal lets users access and manage their email quarantine, allowing them to release messages inadvertently marked as spam. They can also create and manage email-sender allow/block lists to manage their own security.
Sophos Email Self-Service User Portal